The shifting cybersands: Kaspersky shares threat landscape insights and predictions for 2023
Riyadh: Gulf Tech
Kaspersky has shared the evolution of the digital threat landscape in the Middle East, Turkey and Africa (META) region and worldwide during its annual Cyber Security Weekend – META, which took place in Jordan. Kaspersky experts discussed various topics and threats specifically facing enterprises, businesses and industrial organizations and shared threat predictions for the upcoming year. A special focus was made on security for emerging technologies, such as robotics, IoT, and critical industry-specific threats – these technologies should be addressed through a secure by design approach such as Kaspersky’s Cyber Immunity.
“Today’s hyper-connected world requires us to reconsider the way we do cybersecurity. We need to shift toward a more reliable approach – one with no room for error. This is why we’re working on developing Cyber Immune products with “innate” protection against cyberthreats. Most attacks on the Cyber Immune systems are ineffective. It’s through events like this one in Jordan that we’re able to share our innovations and educate our audience about a safer and more resilient digital world where Cyber Immunity is the new norm,” said Eugene Kaspersky, CEO of Kaspersky.
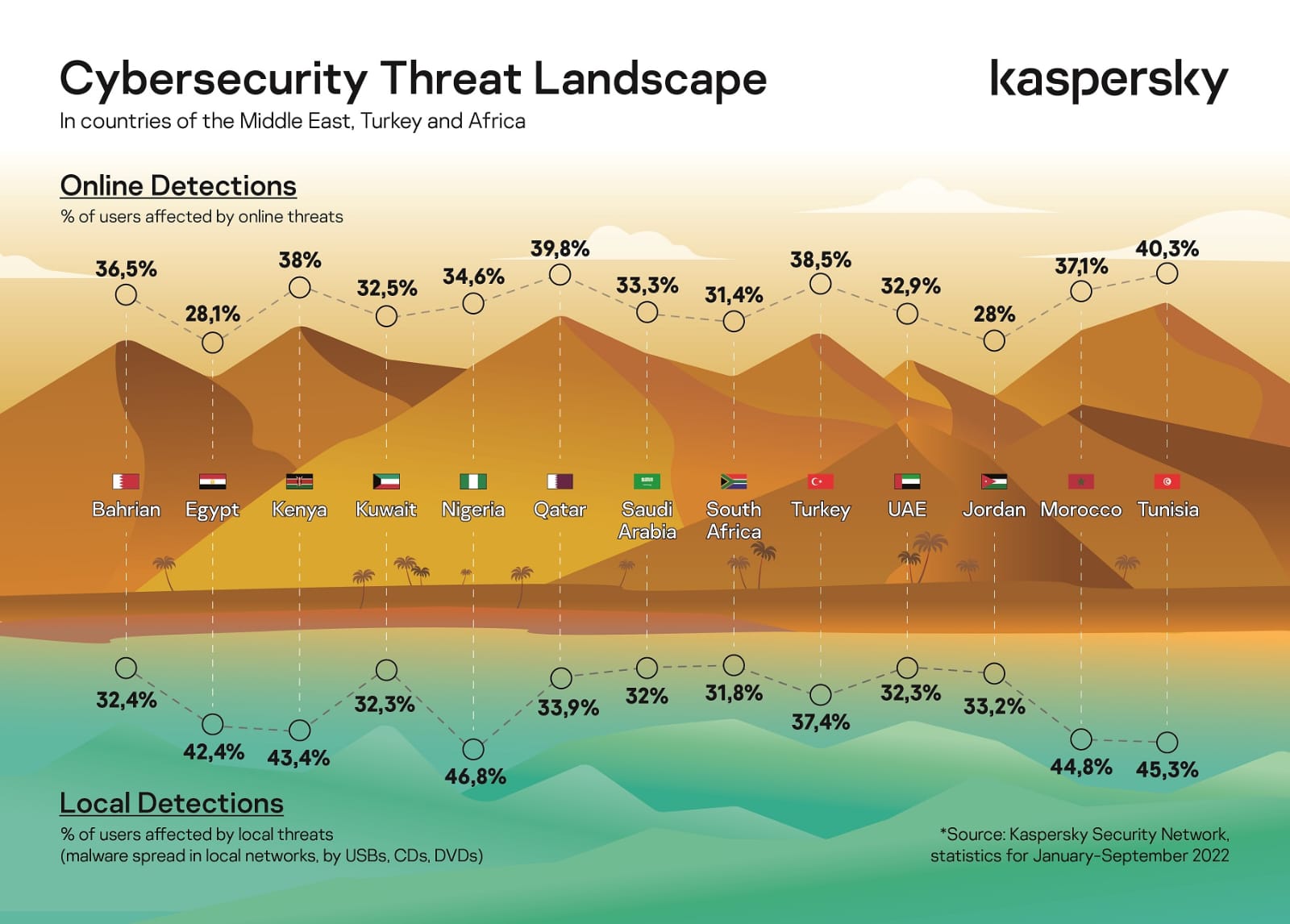
During the event, experts shared the latest threat statistics from the region. According to Kaspersky Security Network statistics, about every third user in the META region was affected by online and offline threats in January-September 2022. Focusing on the Middle East, Qatar had the highest number of users affected by online threats (39.8%). Followed by Bahrain (36.5%), Saudi Arabia (33.3%), UAE (32.9%) and Kuwait (32.5%). Fewer users were affected in Egypt and Jordan (28.1% and 28% respectively).
The highest numbers of offline threats in the Middle East were reported in Egypt (42.4%), Qatar (33.9%), and Jordan (33.2%). Bahrain (32.4%), UAE (32.3%), Kuwait (32.3%) and Saudi Arabia (32%) had the lowest numbers of affected users in the Middle East by local threats.
Increase in APT intrusions in the META region
In 2022 there has been an increase in the number of persistent and sophisticated attacks targeting various states in the META region. Starting from the most recent threat actor Metador targeting telecommunication companies, HotCousin expanding its operations to this region, the numerous campaigns deploying various IIS backdoors, DeathStalker and Lazarus attacking multiple industries there and a mysterious SSP-library backdoor discovered on governmental and non-profit entities, there were several new threats active in the region over the last year.
2023 predictions – what’s next?
The 2023 forecast is based on Kaspersky expertise and the activity witnessed this year while tracking more than 900 APT groups and campaigns.
• The next WannaCry and drones for proximity hacking. Statistically, some of the largest and most impactful cyber epidemics occur every six to seven years. The last such incident was the infamous WannaCry ransomware-worm, leveraging the extremely potent EternalBlue vulnerability to automatically spread to vulnerable machines. Kaspersky researchers believe the likelihood of the next WannaCry happening in 2023 is high. One potential reason for an event like this occurring is that the most sophisticated threat actors in the world are likely to possess at least one suitable exploit, and current global tensions greatly increase the chance that a ShadowBrokers-style hack-and-leak could take place.
Major shifts will be reflected in new types of targets and attack scenarios too, as experts believe next year, we may see bold attackers become adept at mixing physical and cyber intrusions, employing drones for proximity hacking. Some of the possible attack scenarios include mounting drones with sufficient tooling to allow the collection of WPA handshakes used for offline cracking of Wi-Fi passwords or even dropping malicious USB keys in restricted areas in hope that a passerby would pick them up and plug them into a machine.
Other advanced threat predictions for 2023 include:
• SIGINT-delivered malware. One of the most potent attack vectors imaginable, which uses servers in key positions of the internet backbone, allowing man-on-the-side attacks, may come back stronger next year. While these attacks are extremely hard to spot, Kaspersky researchers believe they will become more widespread and will lead to more discoveries.
• The rise of destructive attacks. Given the current political climate, Kaspersky experts foresee a record number of disruptive and destructive cyberattacks, affecting both the government sector and key industries. It is likely that a portion of them will not be easily traceable to cyberattacks and will look like random accidents. The rest will take the form of pseudo-ransomware attacks or hacktivist operations to provide plausible deniability for their real authors. High-profile cyberattacks against civilian infrastructure, such as energy grids or public broadcasting, may also become targets, as well as underwater cables and fiber distribution hubs, which are challenging to defend.
• Mail servers become priority targets. Mail servers harbor key intelligence, making them valuable to APT actors, and have the biggest attack surface imaginable. The market leaders in this industry have already faced exploitation of critical vulnerabilities, and 2023 will be the year of 0-days for all major email programs.
• APT targeting turns toward satellite technologies, producers and operators. There is evidence of APTs being capable of attacking satellites, with the Viasat incident as an example. It is likely that APT threat actors will increasingly turn their attention to the manipulation of, and interference with, satellite technologies in the future, making the security of these technologies ever more important.
• Hack-and-leak is the new black. The new form of hybrid conflict that unfurled in 2022 involved a large number of hack-and-leak operations. These will persist in the coming year with APT actors leaking data about competing threat groups or disseminating information.
• More APT groups will move from CobaltSrike to other alternatives. CobaltStrike, a red-teaming tool, has become a tool of choice for APT actors and cybercriminal groups alike. It has gained significant attention from defenders, making it likely that attackers will switch to new alternatives such as Brute Ratel C4, Silver, Manjusaka or Ninja, all offering new capabilities and more advanced evasion techniques.